The Dell Wyse team has recently launched support for Windows Virtual Desktop(WVD) on Dell Wyse ThinOS 9.1. This is big news as it allows us to use a non-Windows thin client endpoint to connect to your WVD environment! Microsoft posted a quick announcement about this as well here.
I’ve covered some details about the configuration below and you can access the official documentation here;
- ThinOS 9.1 & WVD product summary noted here
- ThinOS 9.1 administrators guide here, release notes here, & 8.6 to 9.1 migration guide here
- Note – If you are still on ThinOS 8.6 you can learn how to upgrade to 9.x here
The configuration for ThinOS & WVD is pretty straightforward with the only configuration needed is a Wyse Management Suite (WMS) policy to specify Windows Virtual Desktop under the broker setting which is shown below.
Note – by default, the WVD client package is pre-installed on 9.1 but incase it’s not or you’re looking for latest you can get from support.dell.com under drivers for your model, for example 5070, search for ‘wvd’.
- In WMS, edit your ThinOS 9 policy and browse to ‘Advanced –> Broker Settings –> Windows Virtual Desktop Settings’ as shown below

2. Under the following section you just need to choose the appropriate WVD deployment model you are using. You will chose either the latest WVD ARM (Azure Resource Manager) based deployment model or the ‘classic’ WVD non ARM based deployment. In my testing, I am using the Azure portal ARM based deployment so I selected the (ARMv2) option. When you are done, click ‘Save & Publish’.
3. Also under, Broker Settings\Global Broker Settings set to – “Windows Virtual Desktop” on your policy as shown below:
4. Once the updated WMS policy is received by your device, you should see your new WVD setting reflected on your device as shown below 
4. Once the devices reboots, you should be prompted with the Microsoft Azure AD login screen as shown below  5. At this point you are ready to login into WVD and access your VMs!
5. At this point you are ready to login into WVD and access your VMs! 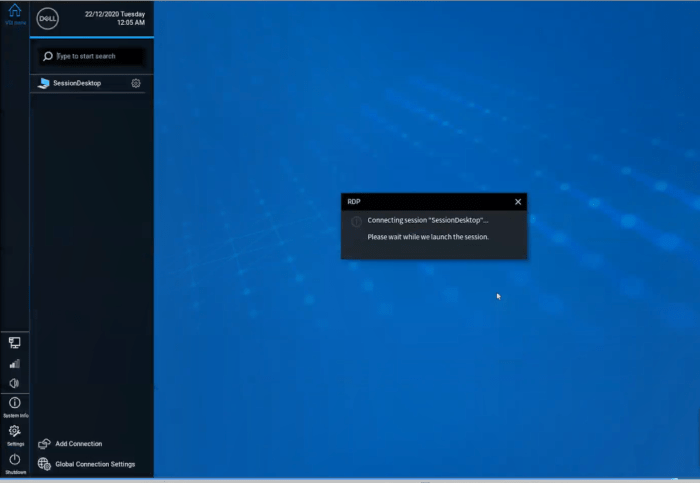 6. In this case I have access to a Windows 10 VM!
6. In this case I have access to a Windows 10 VM! 
Hope you found this helpful!
Additional Resources:
- If you are new to ThinOS 9.1, here is a quick video overview of some of it’s features.
- Looking for more details on ThinOS 9.1? Check out the release notes here
- ThinOS 9.1 release notes discussing WVD setup here & 8.6 vs 9.1 feature comparison here
- Excellent Dell Wyse community located here
- Dell Community forums for ThinOS here
- Microsoft AVD Community forums here
- Great AVD information site & user community here
@chris_messier ~~> Subscribe to blog to get latest updates <~~